THORSwap has launched a bounty program to recover $1.2 million stolen from the personal wallet of THORChain founder John-Paul Thorbjornsen, believed to have been compromised by North Korean hackers.
Key Takeaways
- THORSwap is offering a bounty to the hacker in exchange for the safe return of roughly $1.2 million in crypto assets.
- The victim is reportedly THORChain founder John-Paul Thorbjornsen, whose wallet was breached in a phishing scam traced to a hacked Telegram account.
- PeckShield initially misreported the incident as a protocol hack, later correcting that it was a personal wallet breach.
- THORSwap’s CEO confirmed the protocol was not compromised, aiming to reassure users and protect the platform’s reputation.
What Happened?
A personal wallet tied to THORChain founder John-Paul Thorbjornsen was drained of about $1.35 million after a phishing attack involving a fake Zoom link sent through a hacked Telegram account. The stolen funds included $1.03 million in Kyber Network tokens and $320,000 in THORSwap tokens, which have since been traced to a wallet starting with “0x7Ab.”
The wallet likely belongs to @jpthor who had a private wallet compromised due to a fake meeting scam a few days ago.
— ZachXBT (@zachxbt) September 12, 2025
JP is one of the people whose has greatly benefited financially from the laundering of DPRK hacks/exploits.
So it’s a bit poetic he got rekt here by DPRK. pic.twitter.com/T57RRJ0bbf
THORSwap Issues Public Bounty for Hacker
In an unusual but increasingly common tactic, THORSwap publicly offered a bounty to the attacker. The onchain message read: “Bounty offer: Return $THOR for reward. Contact contact @ thorswap.finance or THORSwap discord for OTC deal. No legal action will be taken if returned within 72 hours.”
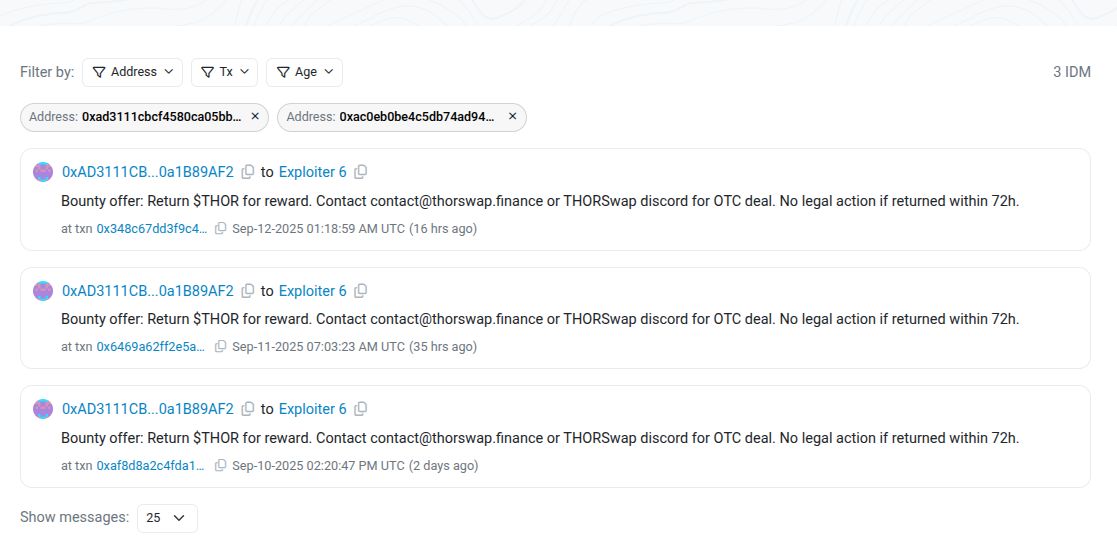
These messages were flagged by PeckShield, which initially claimed that THORChain itself had suffered an exploit. However, this was later corrected after THORSwap CEO “Paper X” and the THORChain team clarified that the protocol remained secure. The breach affected only an individual’s wallet, not the decentralized infrastructure of THORChain or THORSwap.
Hacker Gained Access Through Sophisticated Phishing Scam
Blockchain investigator ZachXBT identified the exploit as originating from a phishing message sent via a compromised Telegram account, allegedly belonging to a friend of Thorbjornsen. The message contained a link to a fake Zoom meeting, which when clicked, compromised an older MetaMask wallet stored in a logged-out Chrome profile and secured via iCloud Keychain.
Thorbjornsen acknowledged the attack on social media, stating, “Had an old MetaMask cleaned out,” and added that attackers may have used a zero-day exploit to access sensitive key material. He emphasized that threshold signature wallets splitting key shares across multiple devices may be the only real protection against such advanced attacks.
No Protocol Compromise, But Big Lessons for Security
While the stolen funds were quickly traced and partially converted to Ethereum, THORSwap’s infrastructure was not impacted, and the team took immediate steps to communicate transparently with the community.
- THORSwap’s CEO stressed: “This is just a bounty requesting for return of stolen assets. No protocol (THORChain or THORSwap) were exploited.”
- The hacker’s activity was tracked to the wallet dubbed “Exploiter 6,” where most of the stolen assets still reside.
CoinLaw’s Takeaway
In my experience covering crypto breaches, this incident stands out because of how personal and targeted it was. It wasn’t about exploiting code or contracts. It was about exploiting trust. What shocked me most is that even a founder as experienced as Thorbjornsen could be tricked with a simple link. I found THORSwap’s response surprisingly mature. Offering a bounty without legal threats sends a message: this is about recovery, not revenge. It also highlights how social engineering has become the most dangerous threat in crypto today. If you’re storing keys in your browser or the cloud, now might be the time to rethink that.